How Do Jammers Work on Wi-Fi?
Wi-Fi jammers can help employers or teachers stop the use of devices on the internet if it becomes distracting. However, Wi-Fi jammers are also notoriously used for disarming many layers of safety protocols. In particular, a Wi-Fi jammer can disarm an alarm system and other security systems that run on Wi-Fi by disrupting their connection.
Wi-Fi works by sending signals on a frequency to an internet router, either on 2.4Ghz and 5Ghz specifically. Often, people can attempt to improve their Wi-Fi connection by switching between these frequencies and channels on those frequencies. This depends on the fact that an internet user can switch their Wi-Fi connection onto a frequency channel that is less crowded by other devices and Wi-Fi connections.
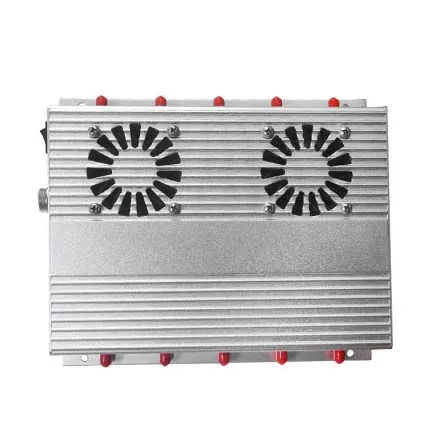
This jammers gps sends out these signals in the hopes that they will overpower Wi-Fi connections and render internet-dependent devices useless.
Can a Phone Signal Booster Cancel Out a Phone Jammer? Determine Why You Are Using Jammer and set up a phone jammer
Find Cell Signal Strength and set up a phone jammer Cell phone jammers Doesn’t End Cell Phone Use Students come to school to learn, whether they like it or not Can a Phone Signal Booster Cancel Out a Phone Jammer? Determine Why You Are Using Jammer and set up a phone jammer Find Cell Signal Strength and set up a phone jammer Cell phone jammers Doesn’t End Cell Phone Use Putting an End to Cell Phone Prison Contraband with Signal Detectors What is a Bluetooth Jammer and How Do I Use it? Main factors affecting cell phone jammer in prison Is it safe to buy a GPS signal jammer online? How to choose cell phone jammer


